Bilibili app 给视频增加播放量
Bilibili app 给视频增加播放量
版本:v6.24.0
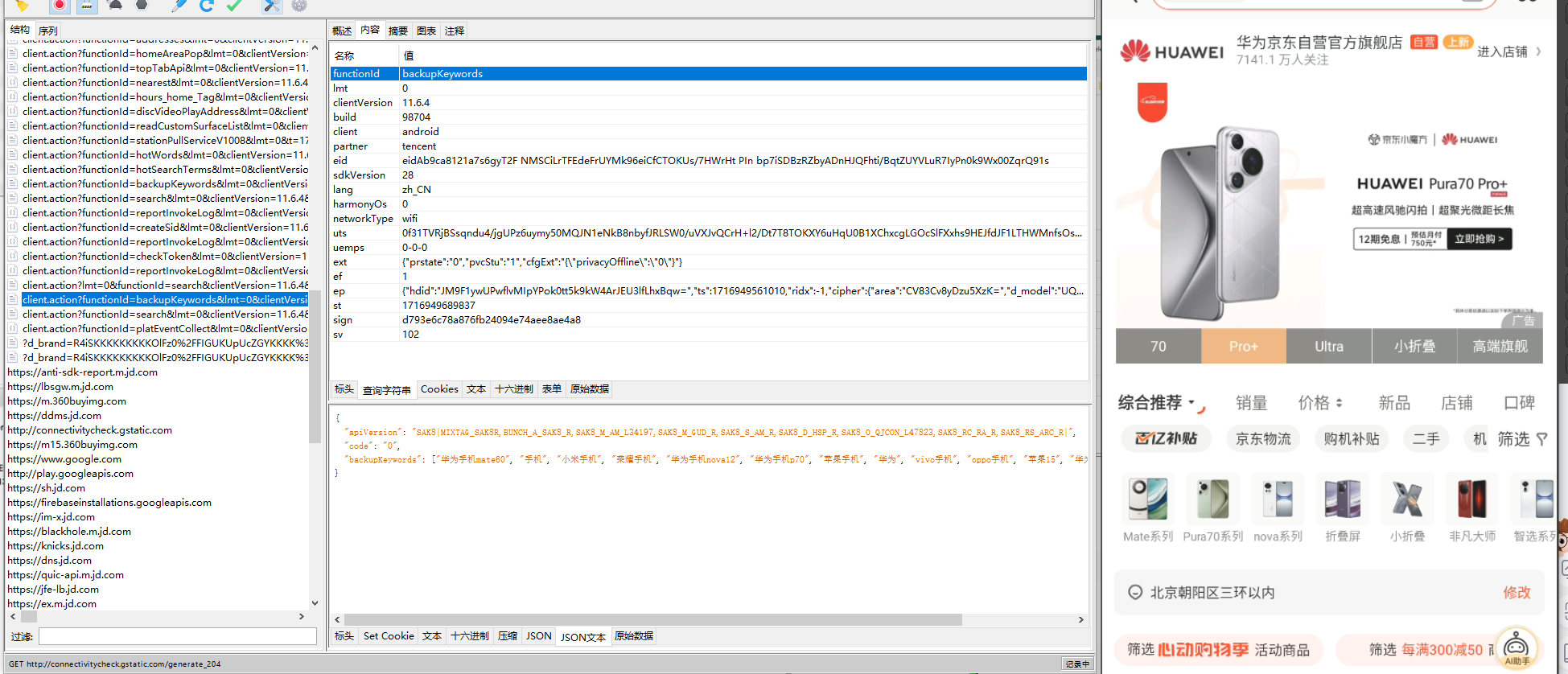
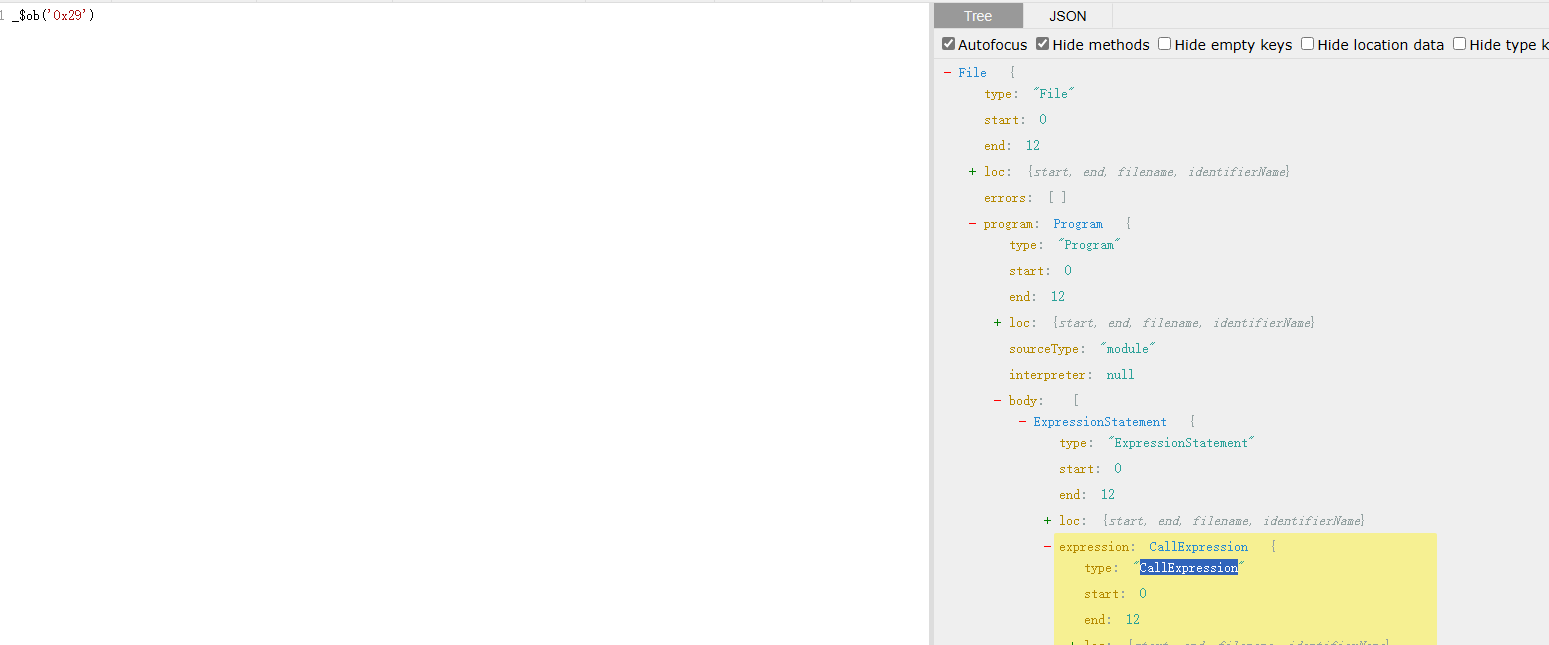
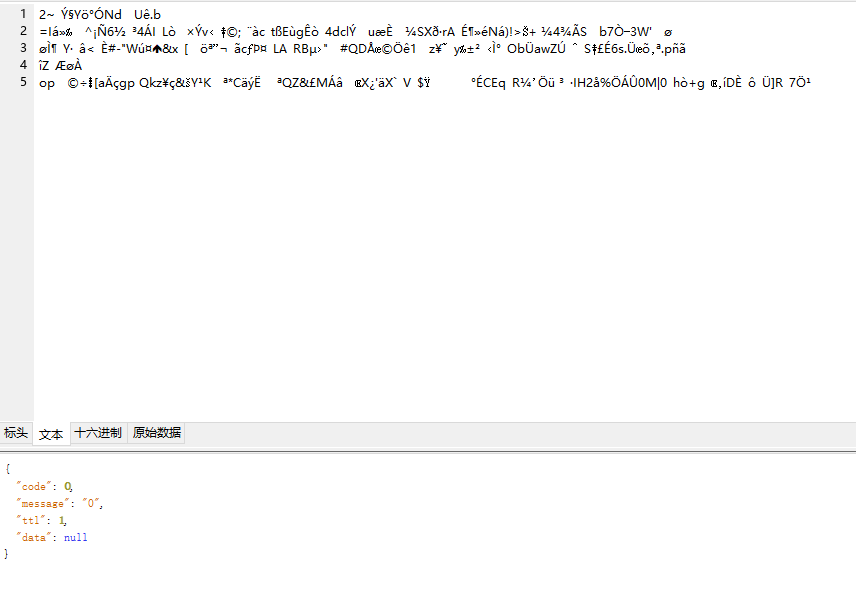
请求体里面应该是做了二进制加密
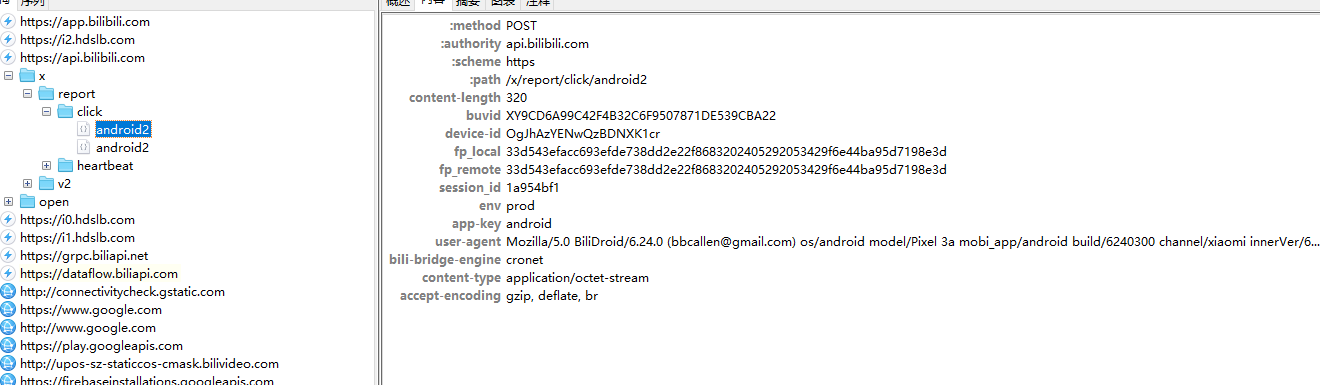
请求头,请求头内容在变更视频的时候 貌似没有变化
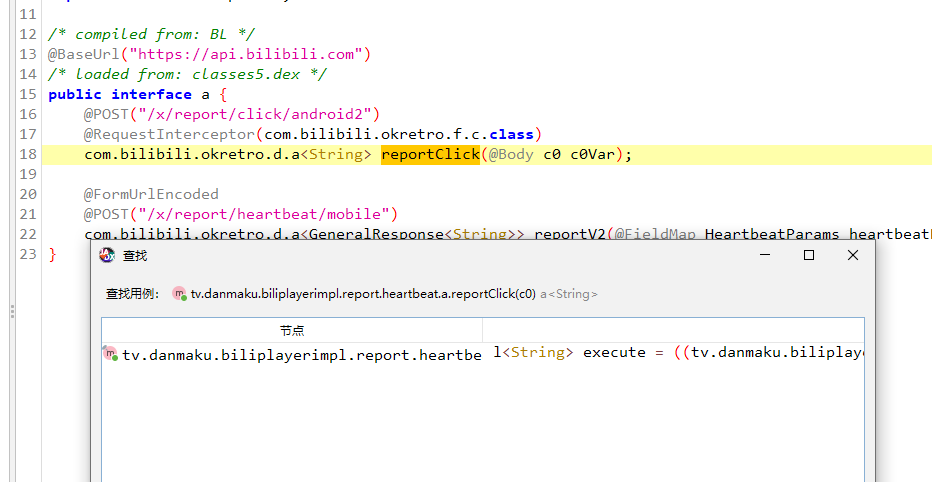
打开jadx反编译搜索
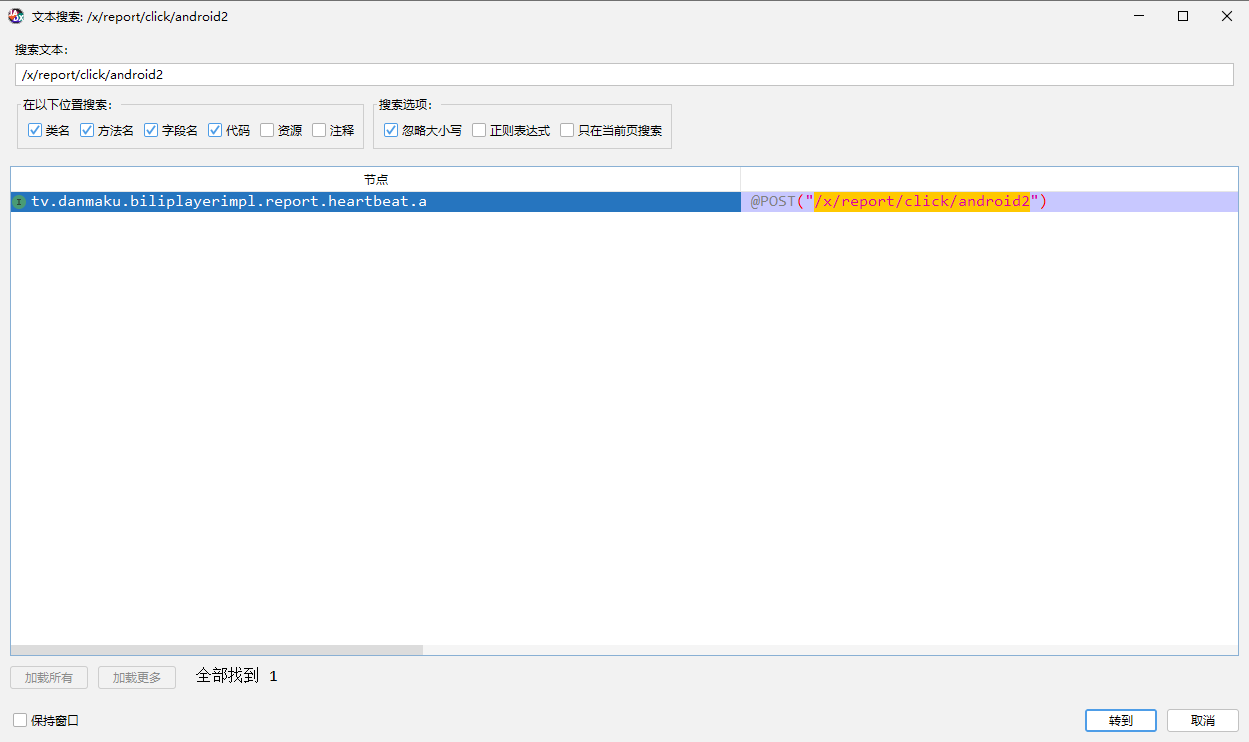
接下来我们要找到 reportClick 方法在哪实现,点击查找用例
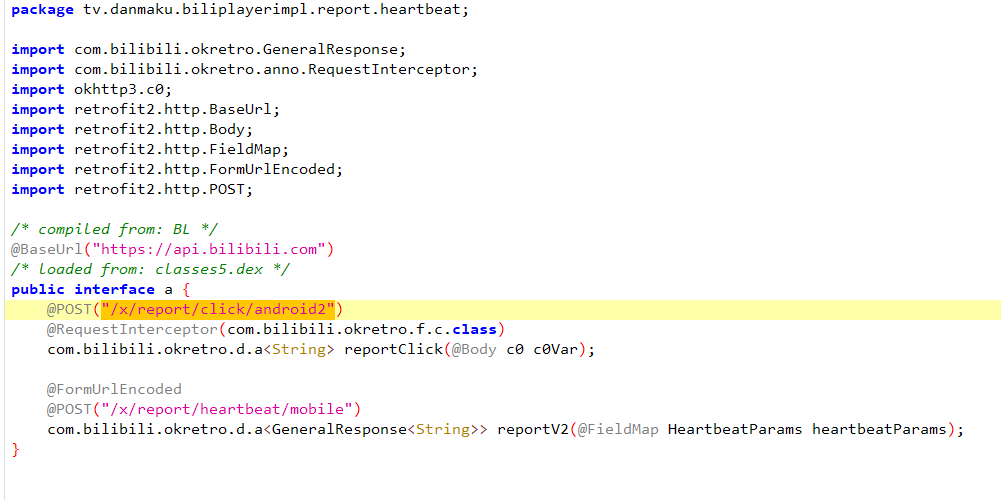
能看到这里实现了一个很标准的retrofit请求,请求体就是 c0 create,看上去里面有很多参数
1 | |
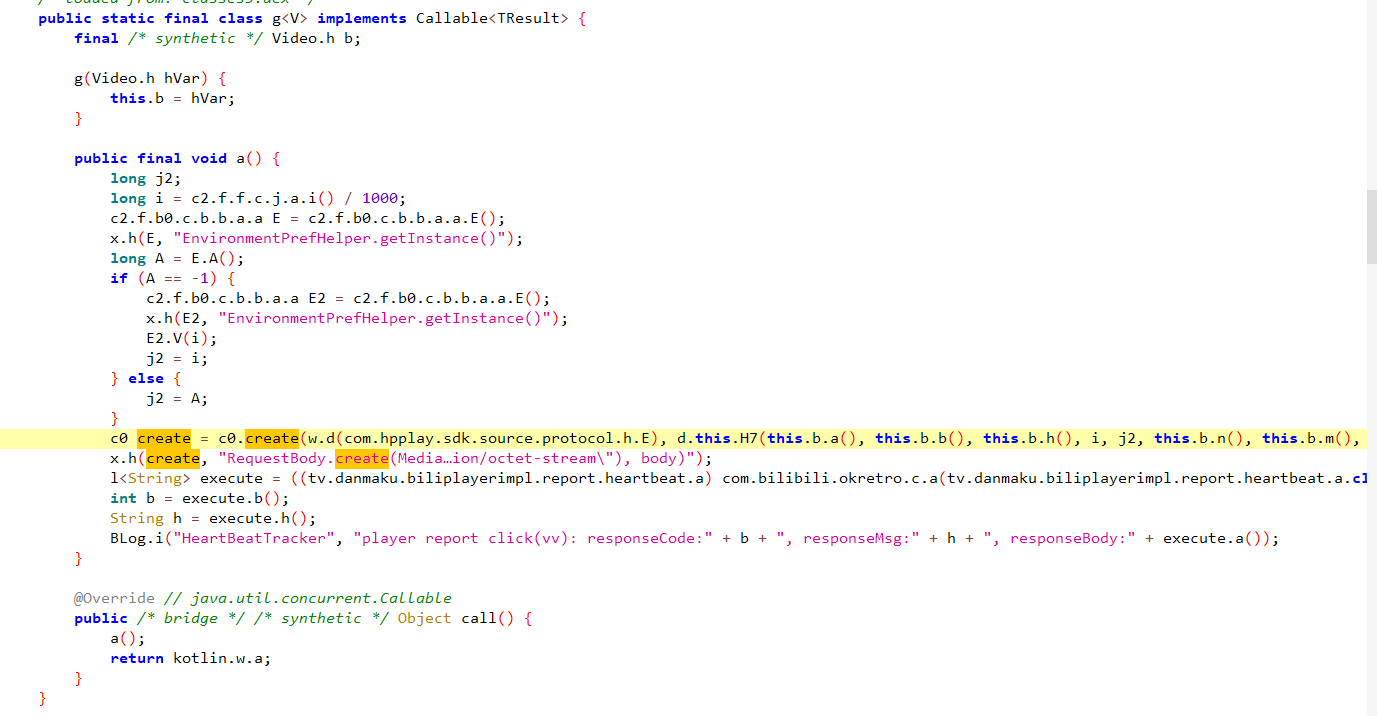
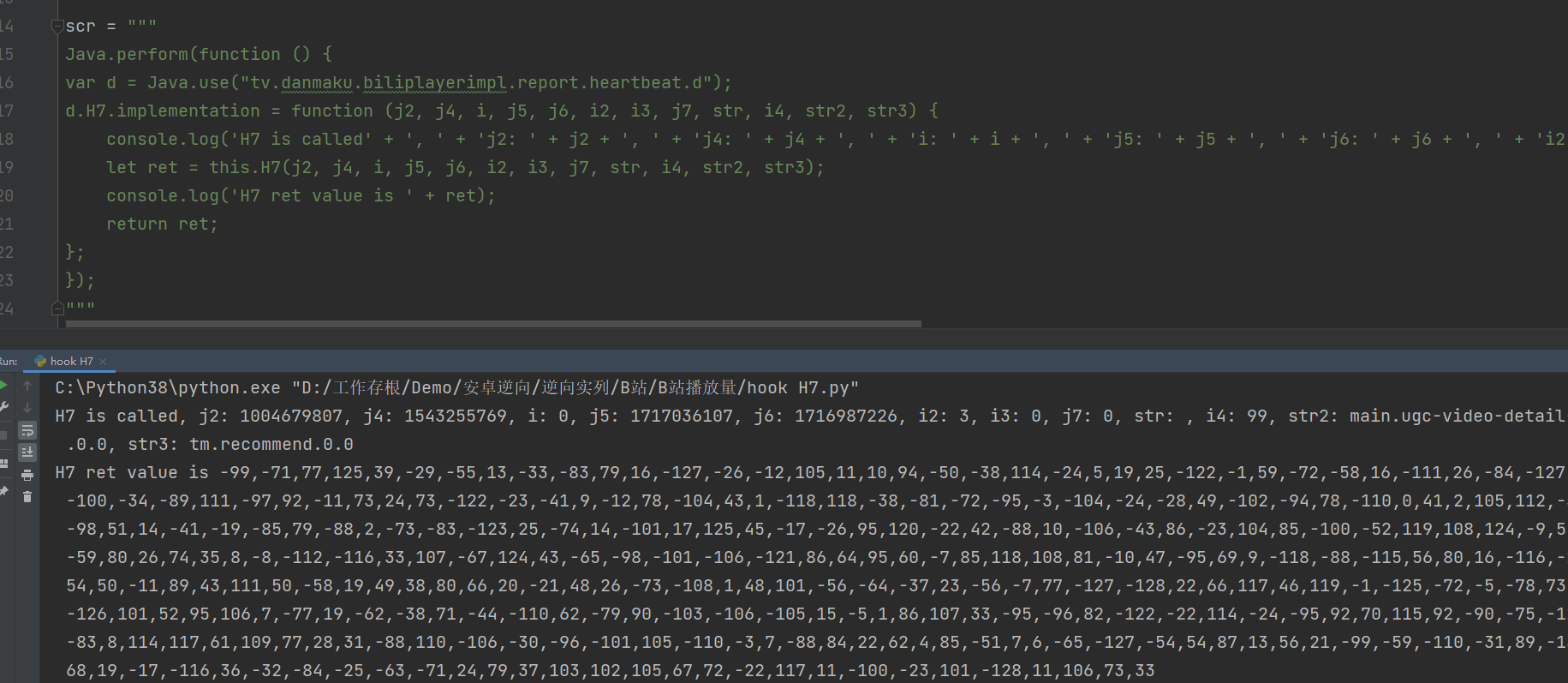
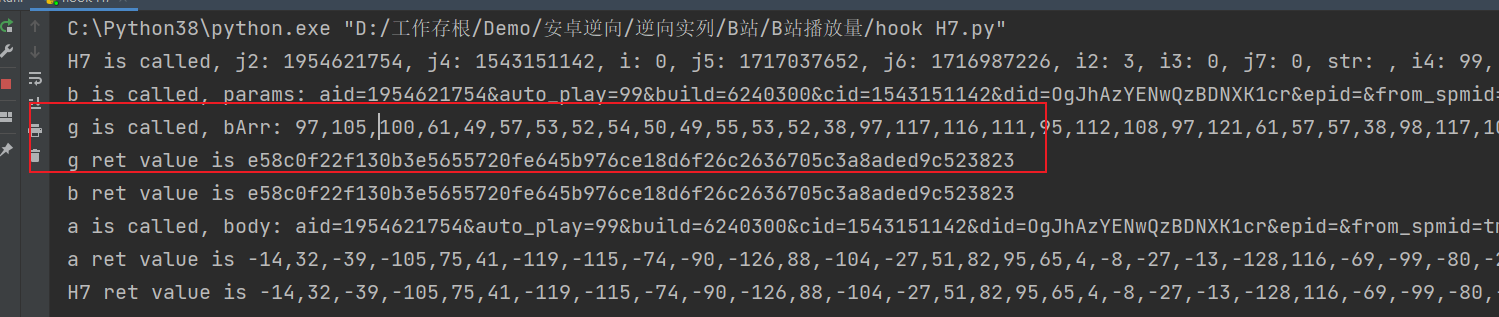
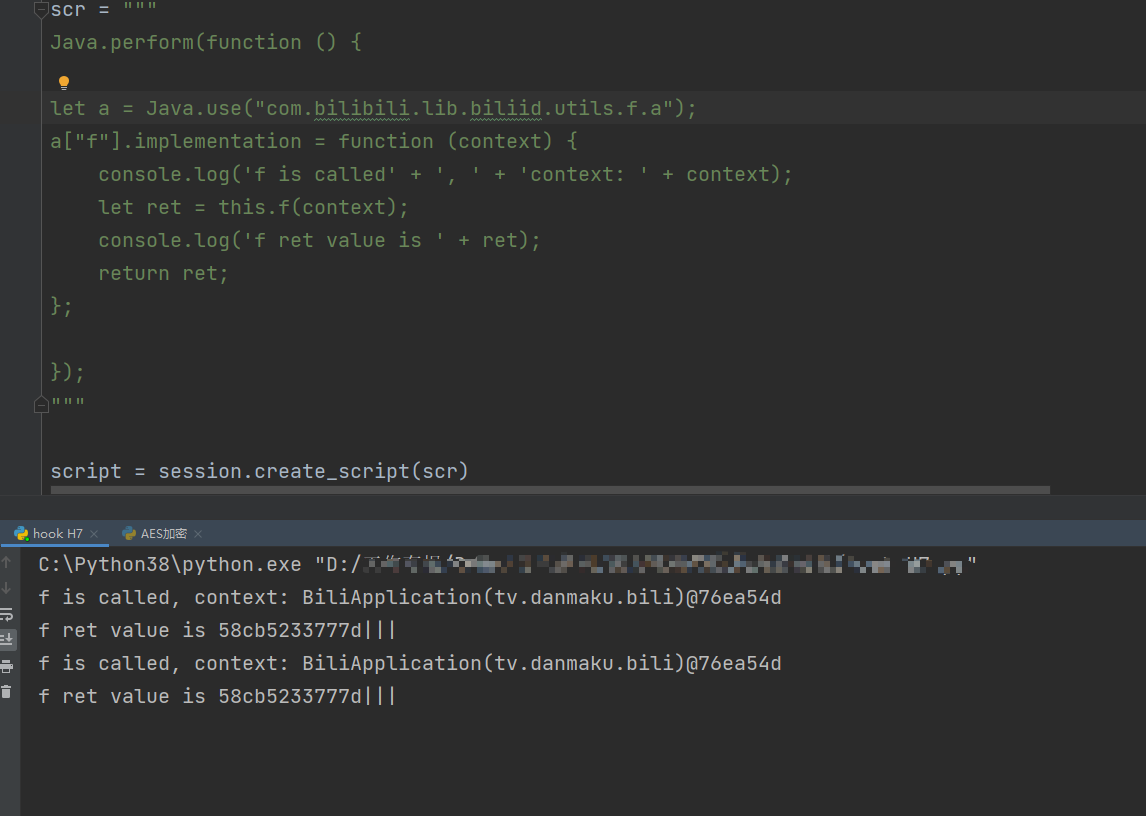
先看一下这个d.this.H7方法,hook一下,hook到之后可以发现 ,传入的参数在这里组成了一个字典,将其组合成字符串后又进行了 t3.a.i.a.a.a.b.e.b 方法加密,我们再看一下这个加密方法
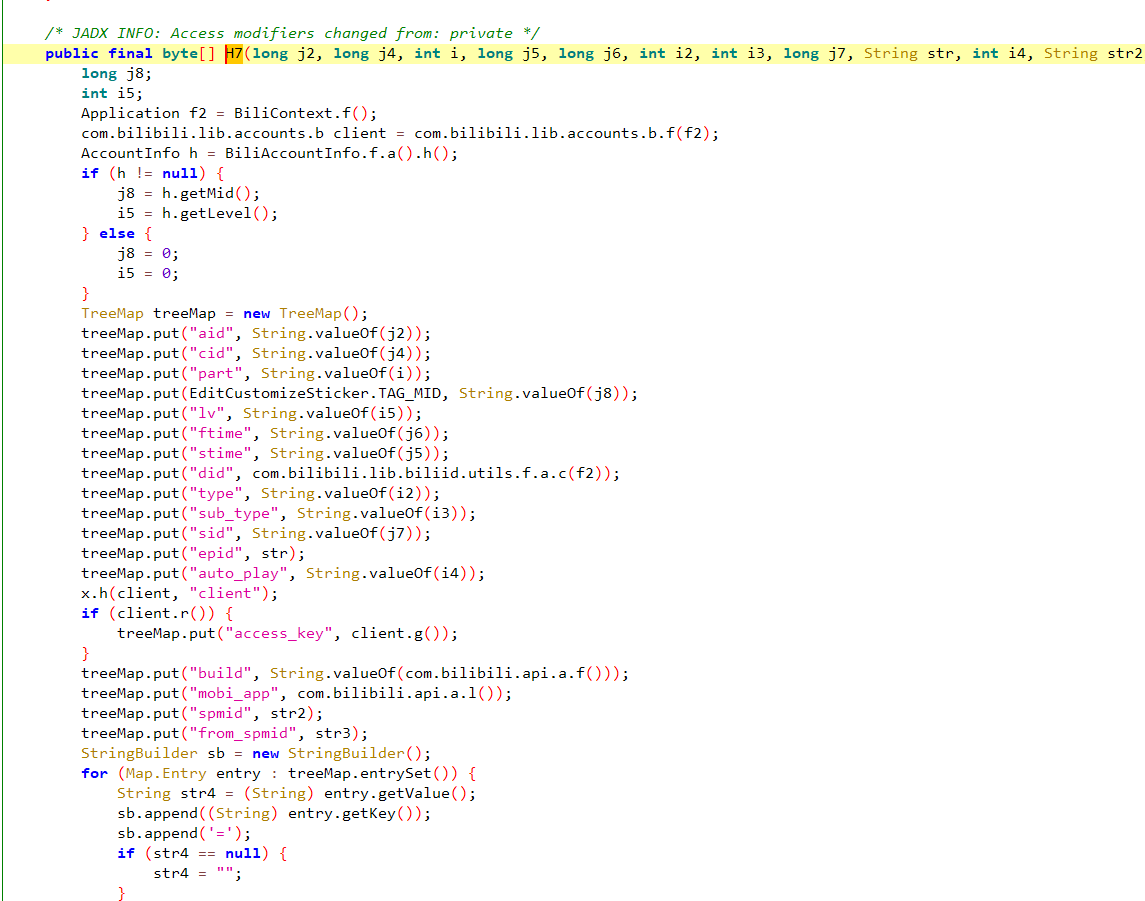
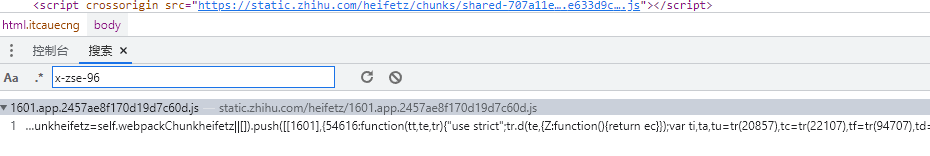
sign
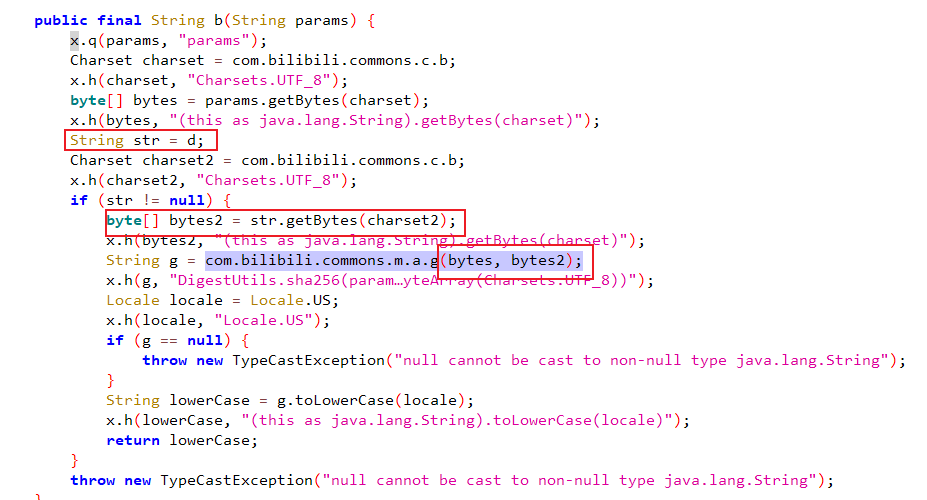
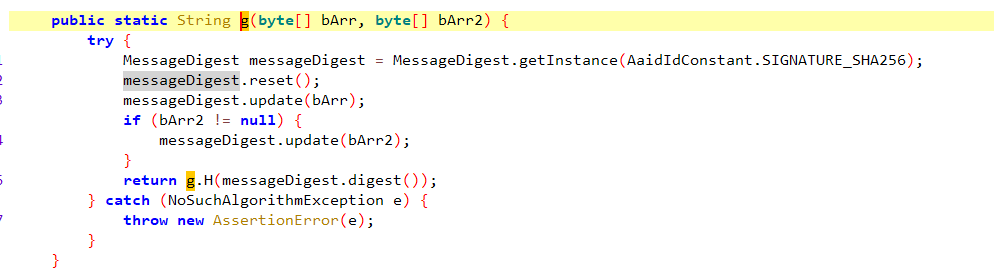
两个加密方法都放在了一起,里面有sha256 和 AES的字眼,其中还有一个 com.bilibili.commons.m.a.g 方法,看上去是sha256加密
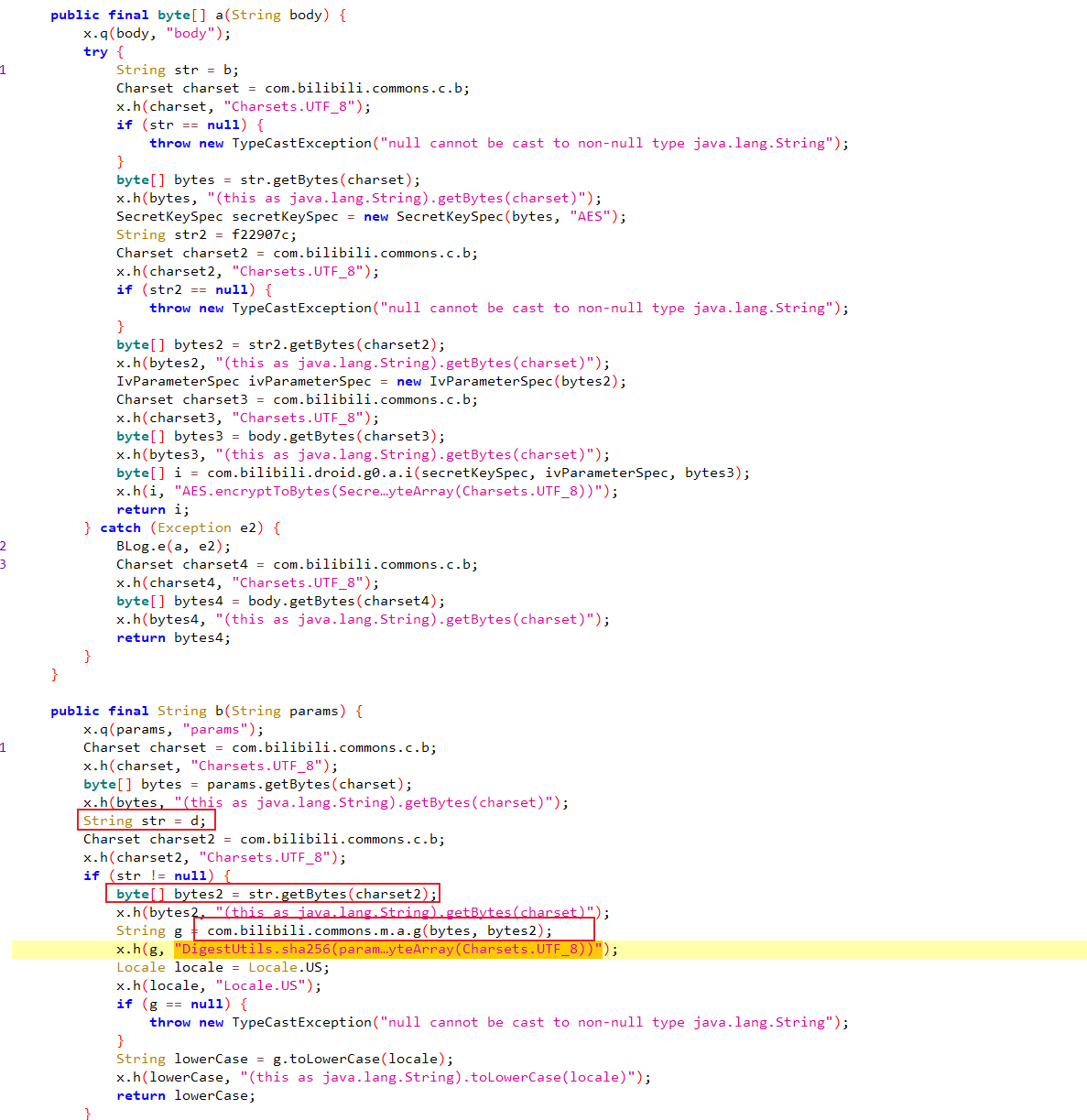
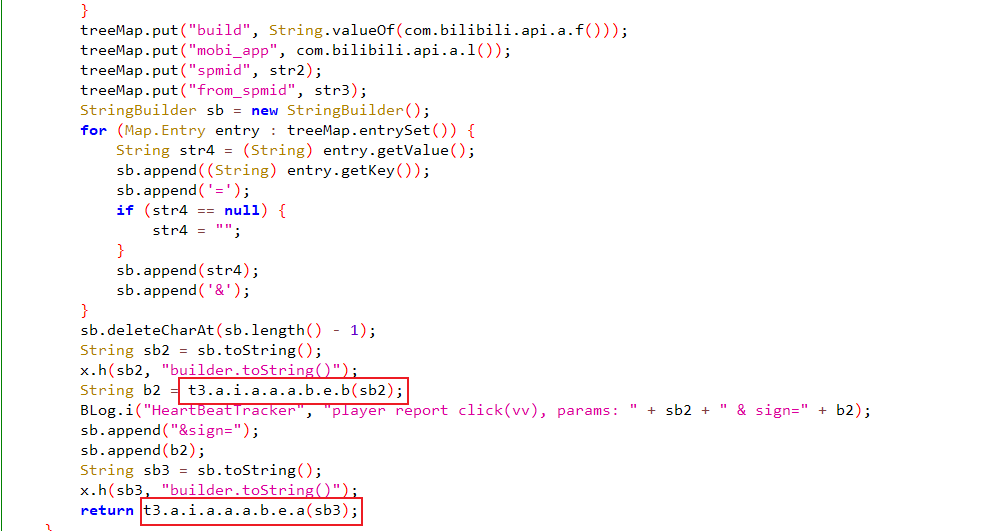
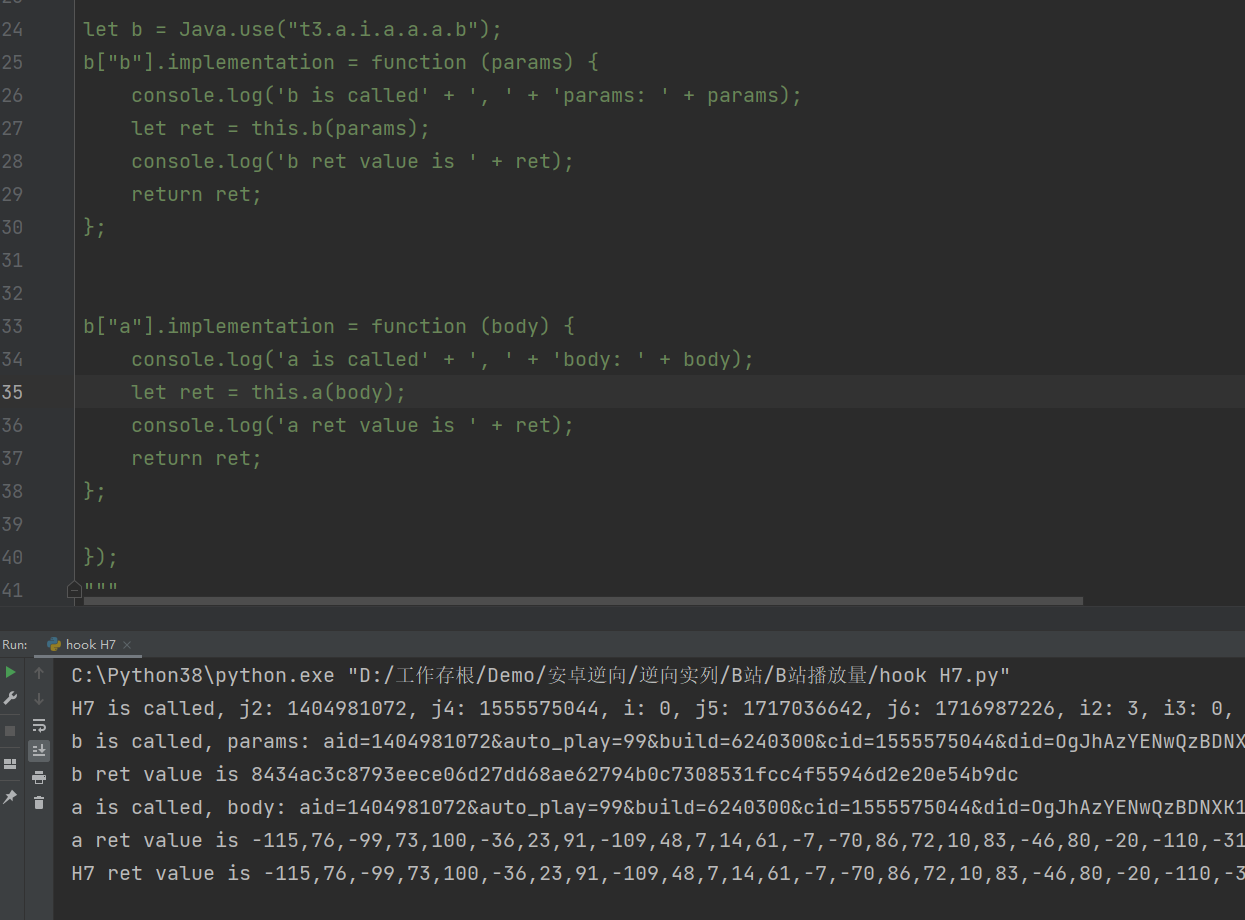
先通过hook a 和 b加密方法,可以看到b方法传入的是参数拼接,然后b加密完成之后成为sign,然后继续拼接到参数后面 &sign=,最后由a方法完成最后加密
1 | |
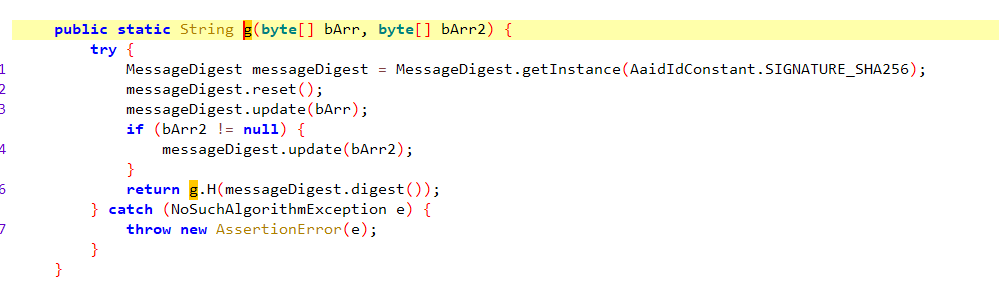
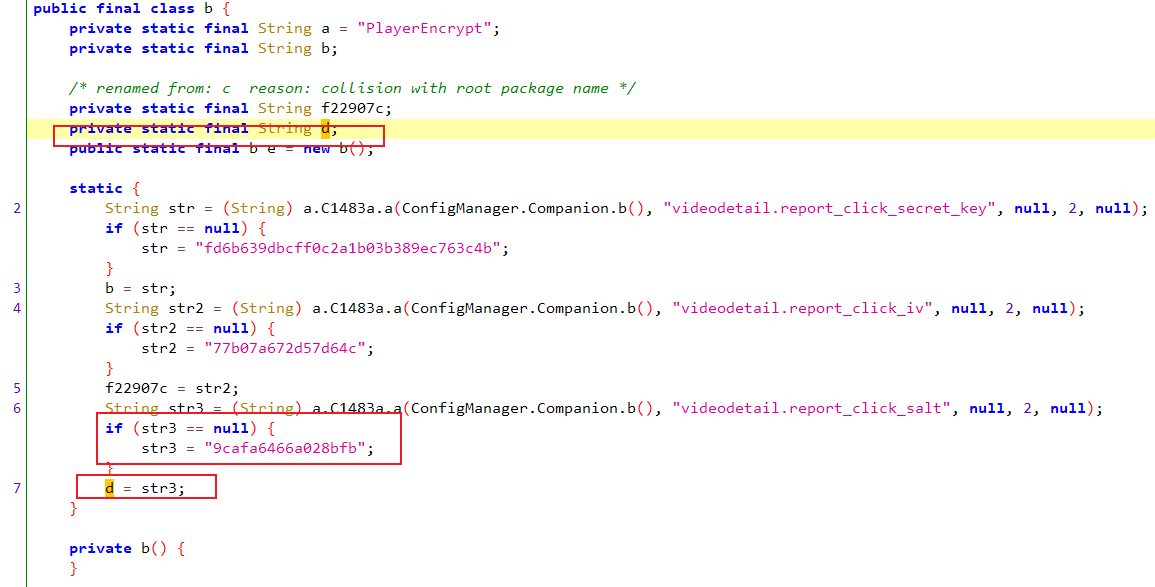
我们再看一下 com.bilibili.commons.m.a.g 方法,这个d 在上面,这个d应该就是g方法的 盐,我们在顺带hook一下g
1 | |
很显然 b方法的核心加密就是在g方法中,这里也可将这些字节转换成字符串,那是根据我们前面代码的推断,g方法传入的第一个参数就是b方法传入的参数拼接转换成的字节数组,第二个参数就是加盐d
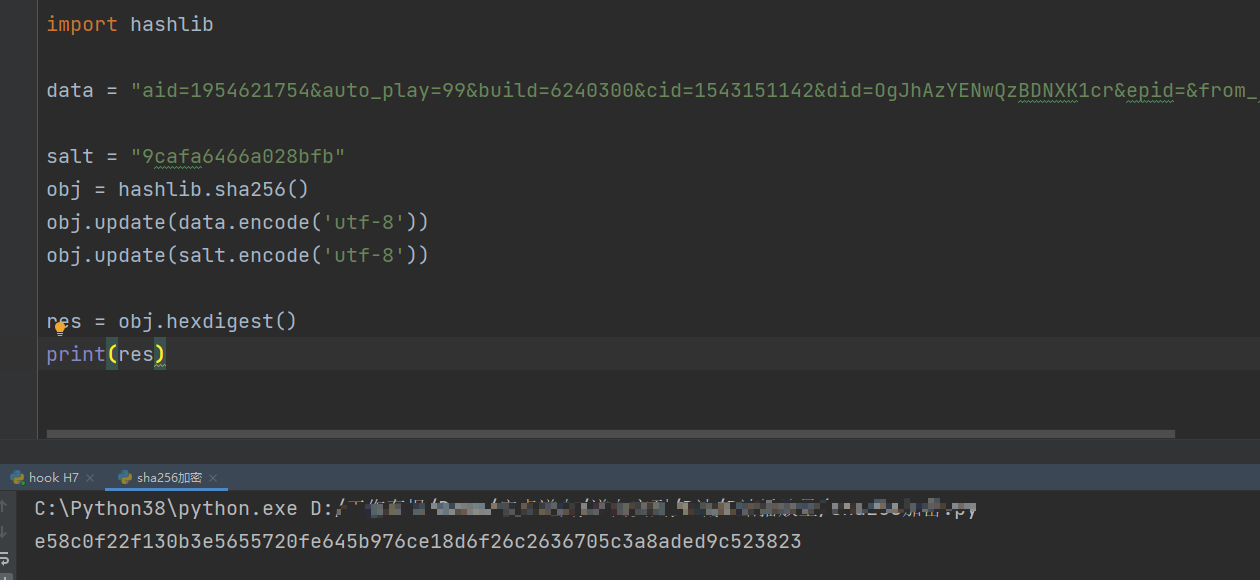
我们可以写一个sha256加密试一下,算法还原后加密结果是一致的,这样我们就得到了sign,继续拼接到参数后面 用a方法加密
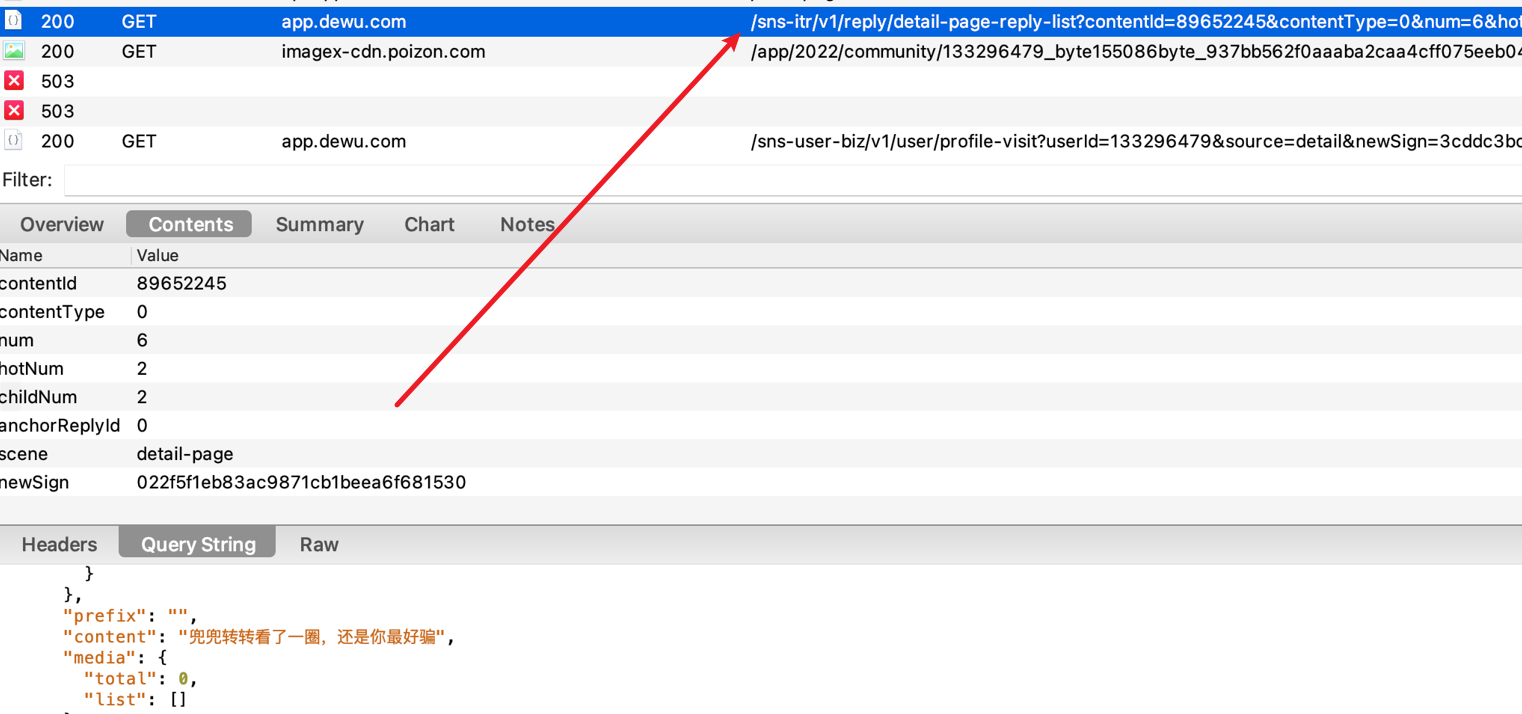
请求体
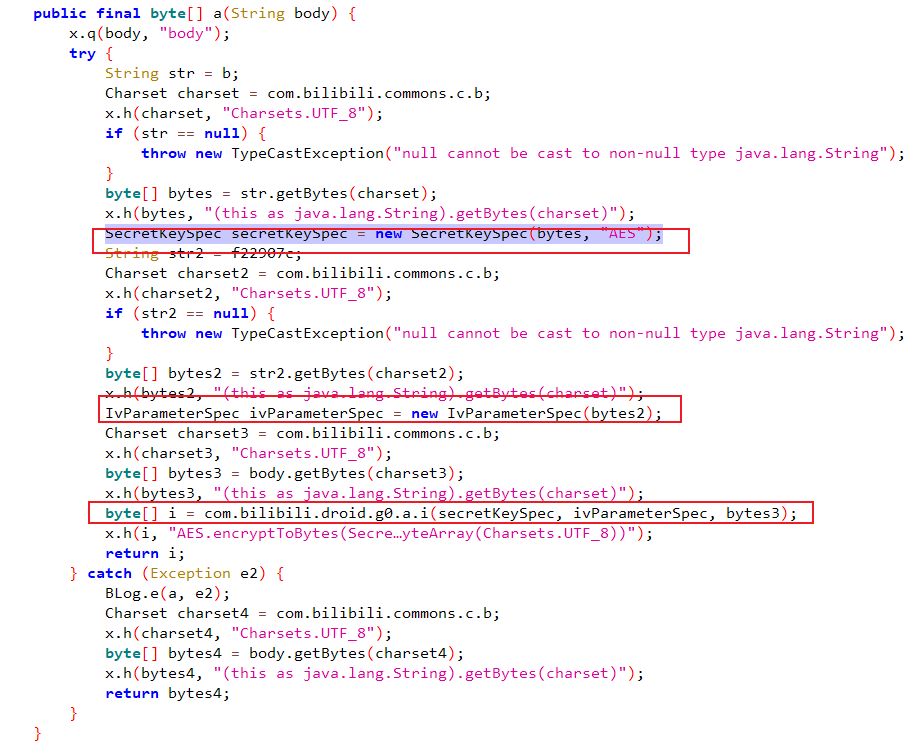
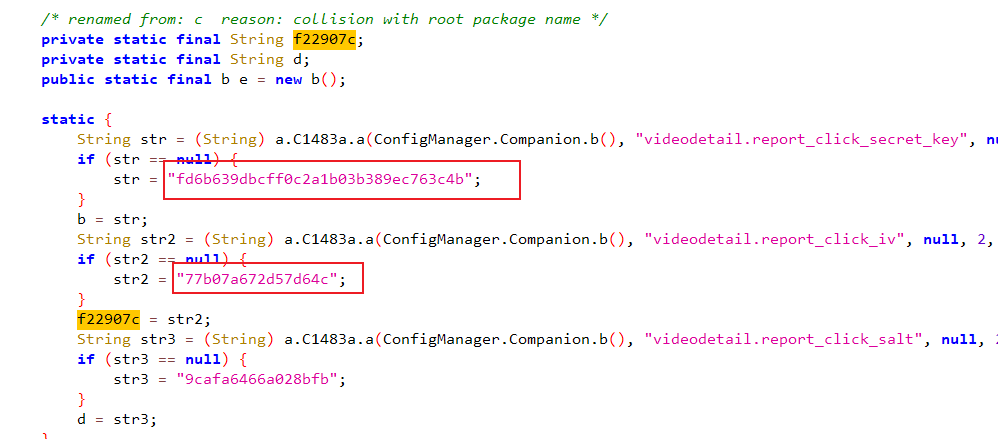
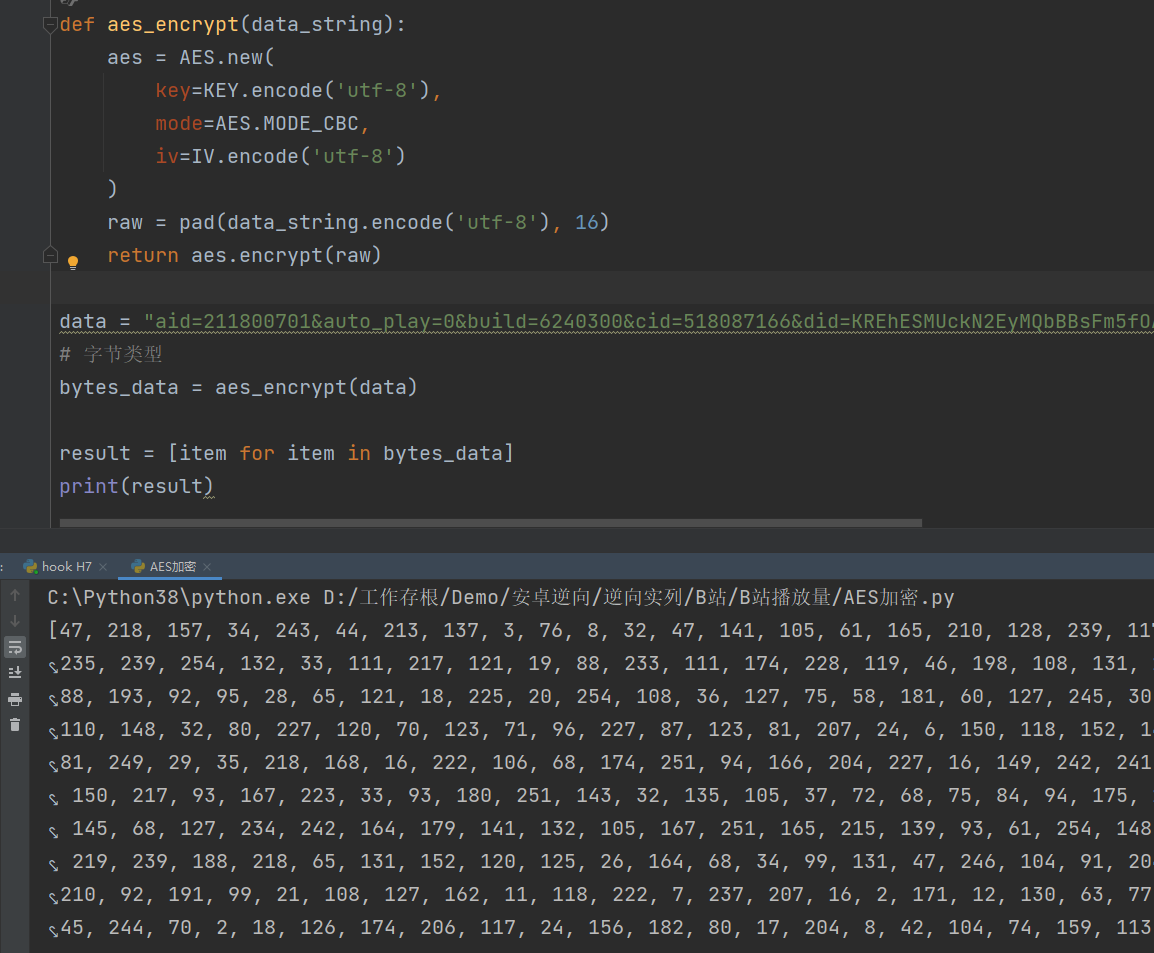
再回到a方法,能看到 key iv,看上去应该就是一个AES加密了,首先看key, key是 str b转换成字节, b在上面,值是 fd6b639dbcff0c2a1b03b389ec763c4b , iv是 str2, str2又是f22907c,f22907c也在上面 值是 77b07a672d57d64c
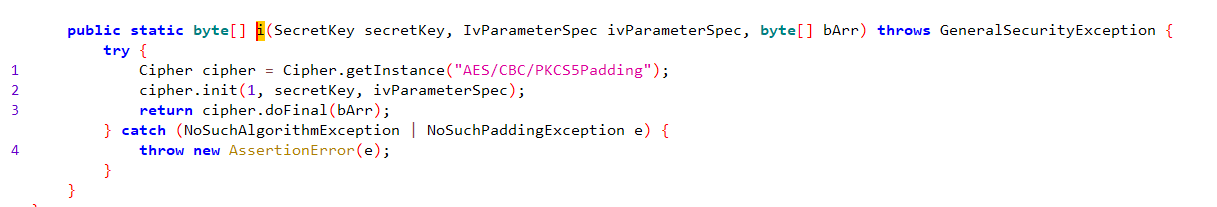
然后再看一下 com.bilibili.droid.g0.a.i 方法
i方法看上去是一个很标准的AES加密,也可以顺便hook一下i方法,这里就不hook了,写一个标准的aes加密看一下结果
设备id
接下来我们要获取这些参数, 我们多刷几个视频,看下哪些固定 哪些需要去逆向,经过多次观察,这里面最重要的还是这个did
1 | |
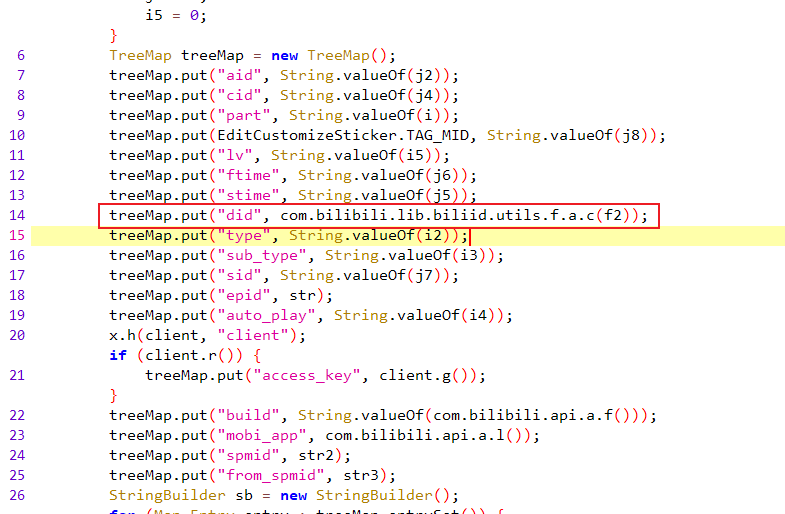
进去看一下这个 com.bilibili.lib.biliid.utils.f.a.c(f2) 这个方法 先去内存中找 f13197c,如果有的话就直接取,没有的话先有 c2.f.b0.c.a.e.k().f(context) 生成,如果还是没有的话就再去找g方法
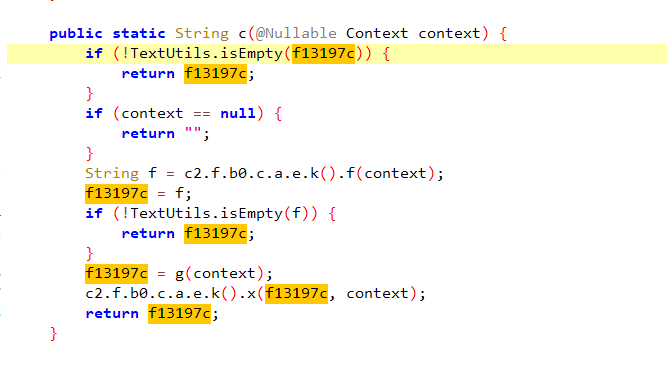
先看一下f方法,入眼就是 SharedPreferences 这里就是从xml文件中提取,如果xml文件中没有的话,那就走g方法
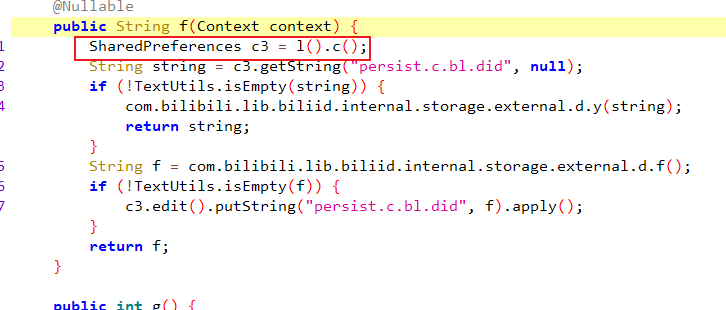
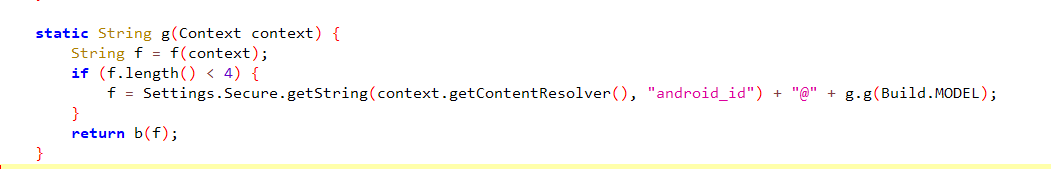
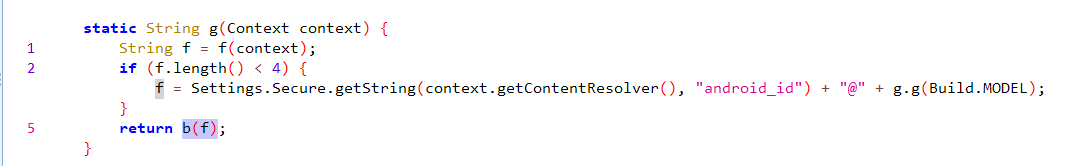
再看下g方法,先调用了一个f方法,如果长度小于4的话,就取做拼接处理,然后再用b方法返回,跟进去看f方法,一直往里跟进,看到c方法
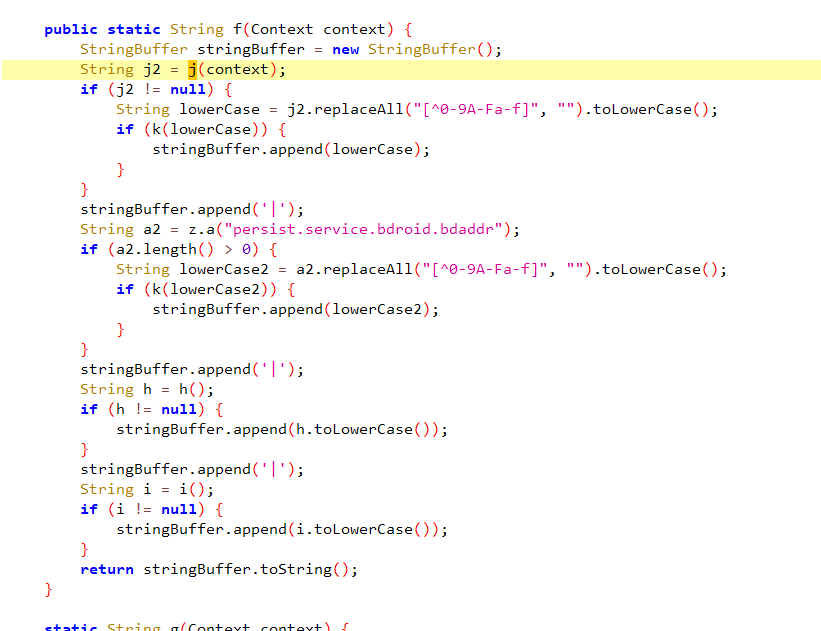
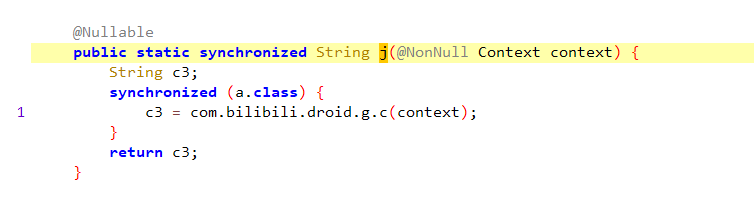
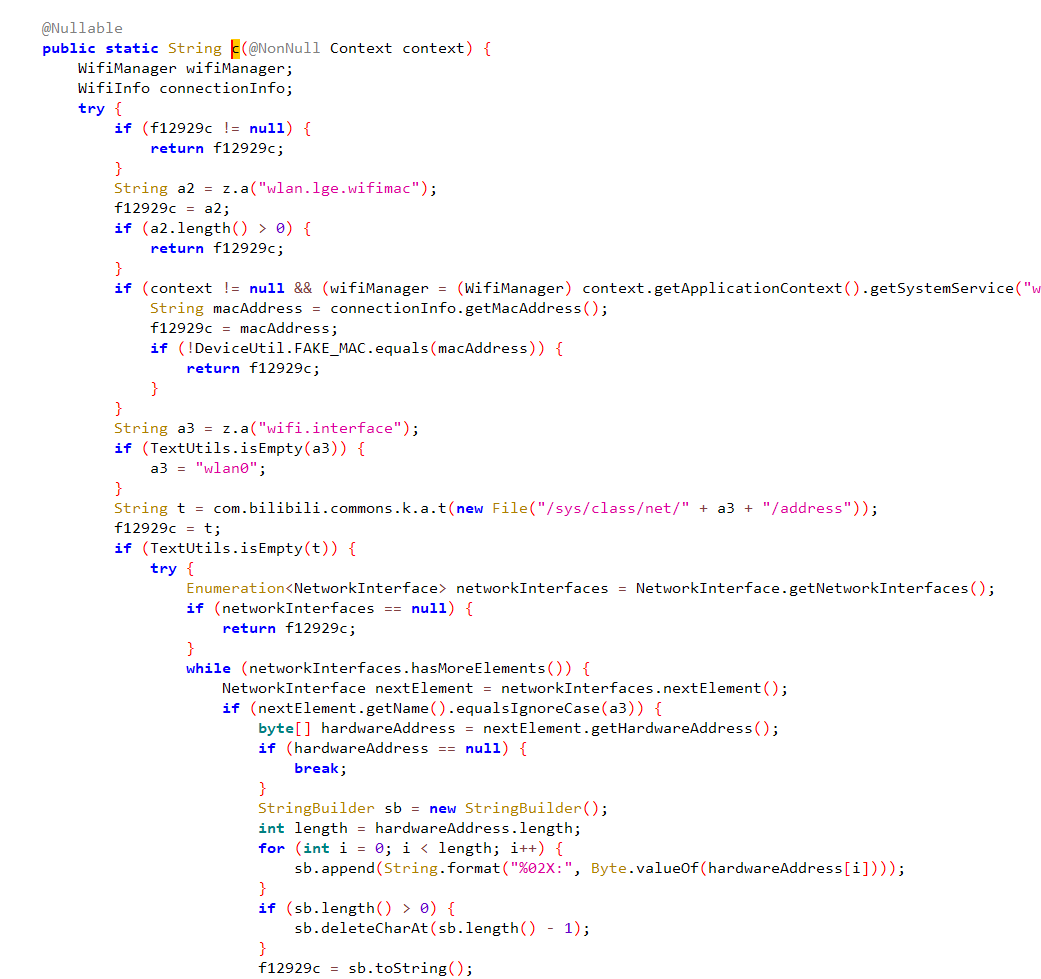
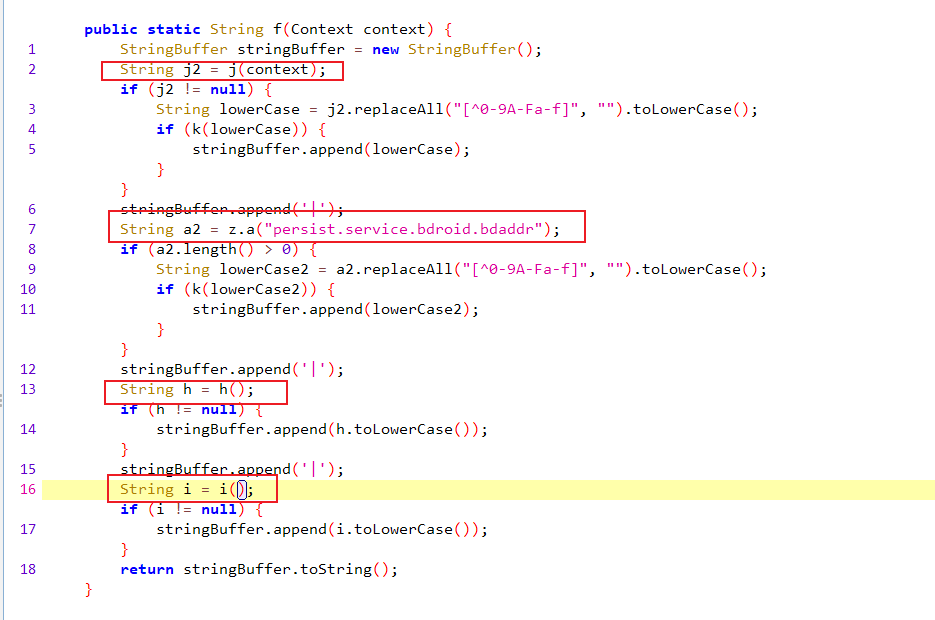
所以一开始j2应该是一个mac地址,c方法读取了网卡信息,后面返回给了j2,然后拼接到了 stringBuffer 中,下面又读取了其它信息,这里需要一个个点进去看一下,我们可以先hook一下f方法,在hook之前需要先退出app 并且清除数据,因为他是先读取内存数据
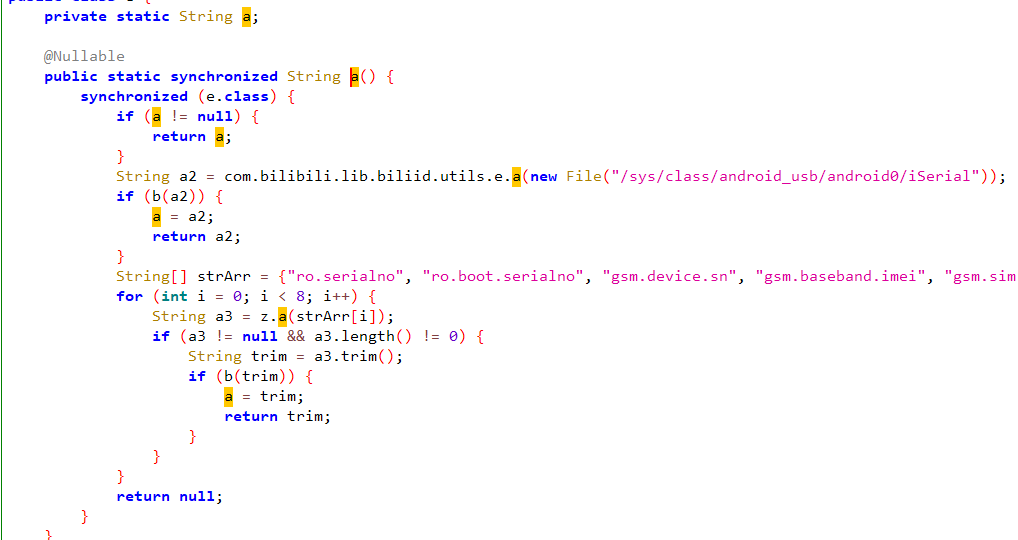
可以看到一共用|拼接了四个字符串,里面都是一些设备信息,我们可以看一下最后一个 i ,往里跟进去的话能看到这里获取到的是手机的sn号,不管是mac地址还是sn号 都是可以通过随机值生成的
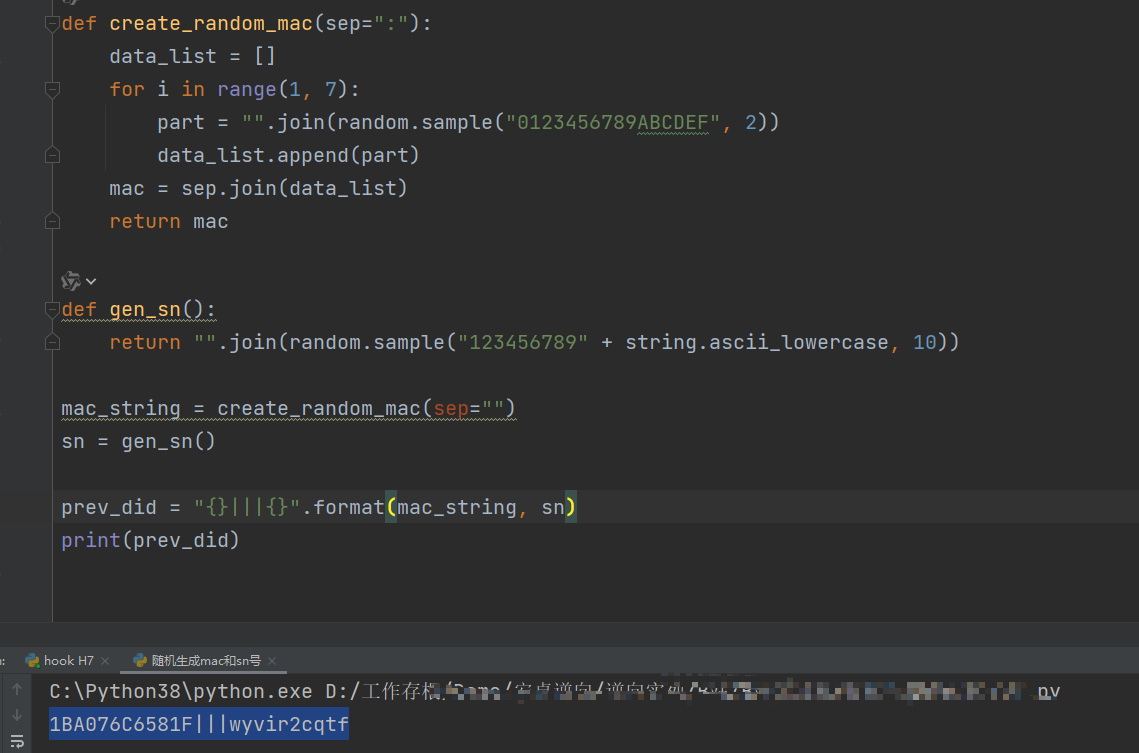
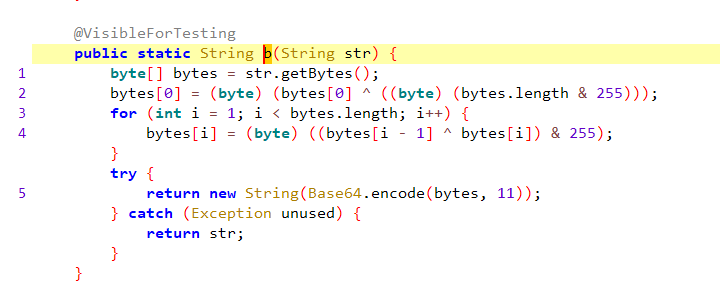
然后回到g方法,最后返回了一个b(f),接下来点进去看下b方法,b方法,先把字符串变成字节, 随后又做了位运算,最后做了一个base64编码,我们用python代码还原一下
最后did的结果
1 | |
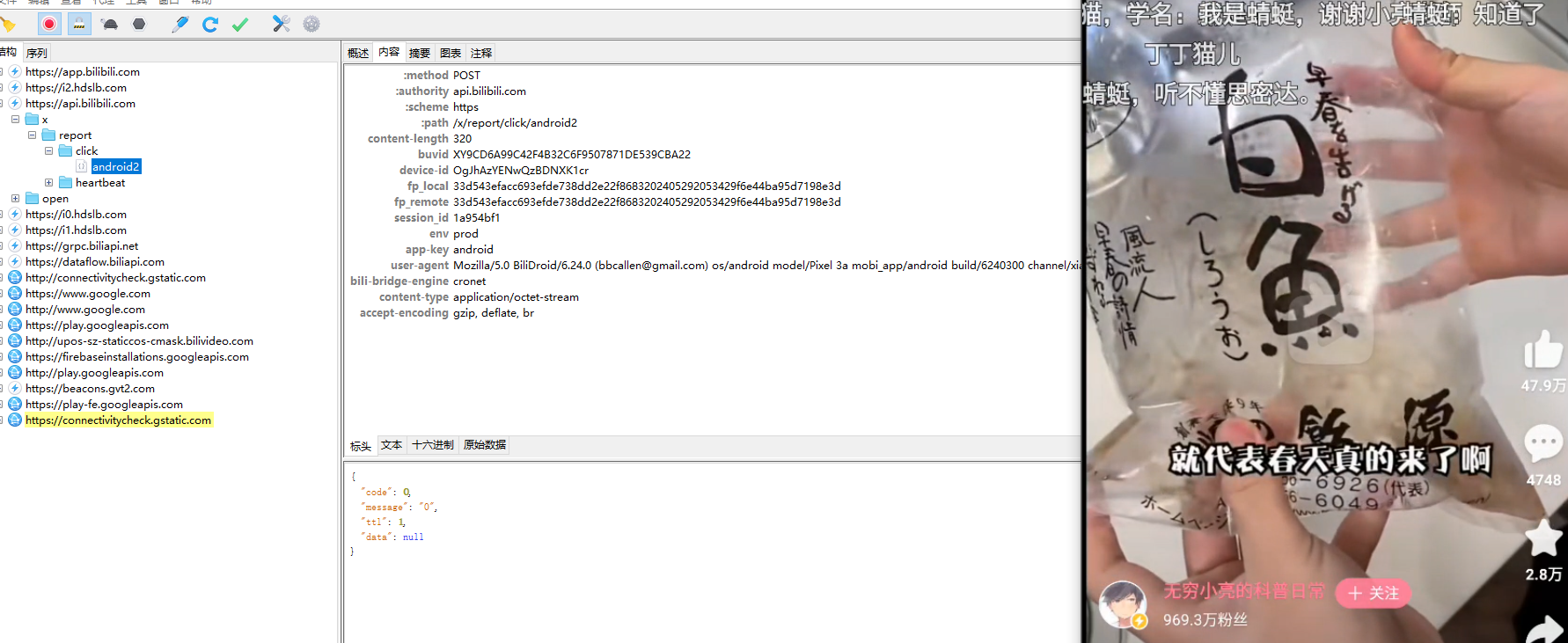
代码整合
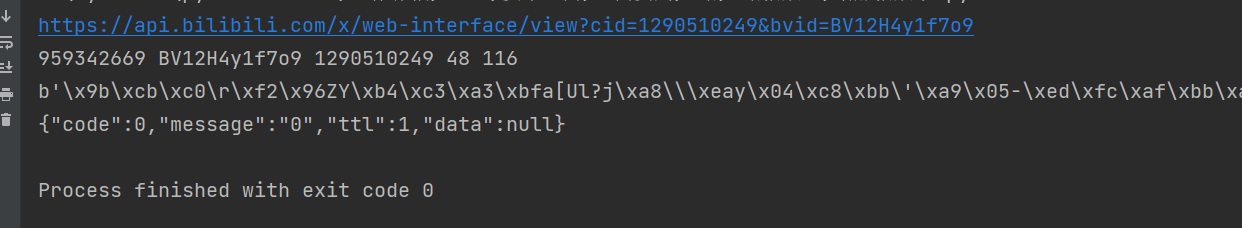
现在sign和did已经获取到了,现在需要获取视频aid 和 cid,这两个id可以通过直接搜索bv号的形式获取目标视频id,接口地址是
1 | |
其实请求头里面还有很多参数可以去逆向,通过一些算法生成,这里就不在深追了
1 | |
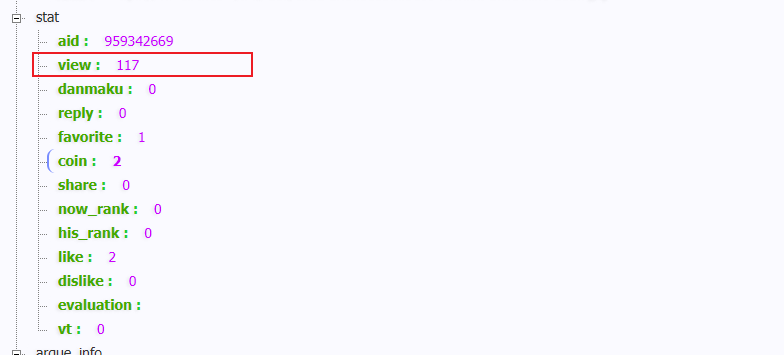
最后也是成功的给视频播放量加了个 1